Typical Raspberry Pi OS, called Raspbian, installation is too cumbersome for a server. You do not even need desktop environment. This part of the webstack tutorial will focus on installing a minimalistic system that can be fine-tuned to your needs. You can use either Windows or Linux. Doesn’t matter as long as you have the means of copying files to an SD card and you are able to connect on the same network both Raspberry and a computer used to administrate your server with.
Getting Raspbian
To get the stock image of Raspbian OS go to The Raspberry Pi Foundation website and download Raspberry Pi OS (32-bit) Lite and unzip the file.
Installing Raspberry Pi OS
Linux
The easiest way to place Raspbian on your SD card is the use of dd command, if you are doing this on Linux I assume you know how to use terminal
sudo dd if=/$path_to_raspbian_img of=/dev/sdX bs=4MB conv=noerror status=progress- bs= tells dd how big should be the write blocks, 4MB is fine
- if= this is the path to Raspbian image file
- of= this is the path to root of your SD card
- conv=noerror ignores errors
- status=progress simply shows progress
Caution! Choosing wrong device will wipe your data, there is no prompt whatsoever! If you specify your hard drive it WILL be erased.
Finding path to SD card in Linux
Run this command
sudo fdisk -lUsually /dev/sda will be your main hard drive and /dev/sdb will be your SD card in case you have a single HDD and only the SD card plugged in.
Devices follow this pattern starting with /dev/
- sda – first physical drive
- sda1 – first partition of the first physical drive
- sda2 – second partition of the first physical drive
- sdb – second physical drive
- sdb1 – first partition of the second physical drive
- etc.
/dev/sdd3 – this would be a third partition of the fourth device
Note that devices differ on the third letter. Don’t make the mistake of writing to /dev/sdA instead of /dev/sdB – this will seriously ruin your evening… Trust me on that
Caution! Remamber that you have to write the image to the device itself and NOT a partition of the card.
Windows
With Windows the easiest way is using Balena Etcher. Just select Raspbian image as source, the SD card as target and confirm that you are sure when the tool asks you.
You can use this tool to make backups of our SD card easily. Trim function allows for use of large cards without bloating the image, which means that 32GB card with 4GB used will take actually 4GB on your hard drive.
Initial Raspbian modification
In case you took the card out after flashing it with Raspbian image put it back in. It will contain two new partitions.
Caution! On Windows you will be able to see only the contents of the boot partition, as it is a fat32 partition.
Caution! Do not format the other partition like Windows suggests! It contains Raspbian and is visible only to machines with Linux filesystem.
Allowing SSH connection to our server
SSH is the preferred way of connecting to the server. You do not need a graphical user interface (GUI) as everything will be done via command line. Foregoing GUI saves space and resources as our Raspberry do not have to encumber the CPU with it. Later we will even remove any packages connected with GUI – why keep what you do not use?
Add an empty file named ssh to boot partition. If using Windows make sure the file is NOT named ssh.txt as windows automatically adds file extensions.
CAUTION If you fail to add this file, SSH interface will not be enabled and you will not be able to connect to your server.
Disabling Wi-Fi and Bluetooth
Since server should have a stable connection we are going to use cable connection instead of Wi-Fi, which we can then disable. If you still prefer using Wi-Fi connection over cable (which you should not), check out the wpa_supplicant.conf instruction below. Since we will not be using Bluetooth we can disable it as well. Wi-Fi and Bluetooth can be enabled and disabled at any time by including or removing the below code in config.txt on boot partition
Navigate to boot partition on your SD card, find config.txt file and add following lines
dtoverlay=disable-wifi
dtoverlay=disable-btBear in mind that disabling Wi-Fi on Raspberry without an ethernet port is a terrible idea. You do need a means of connecting to the internet…
Enabling WiFi with wpa_supplicant.conf file
It is a bad idea to have a server run over Wi-Fi as it is not reliable enough and the bandwidth is limited when compared to cable connection. If you are not concerned with the speed at least think of reliability. Still, if you do not mind, or do not have a choice for some reason, here is how to connect to Wi-Fi.
Navigate to boot partition on your SD card, create a new file and name it wpa_supplicant.conf again mind the extension. Inside place the following code
country=XX
ctrl_interface=DIR=/var/run/wpa_supplicant GROUP=netdev
update_config=1
network={
ssid="$wifi_name"
psk="wifi_password"
}- Substitute XX in country line specifying your country code in ISO 3166-1 alpha-2 standard. Different countries use different frequencies for Wi-Fi and due to legal reasons you need to change it. Also it might not connect if your router has a different country from your Raspberry
- Substitute $wifi_name in ssid line with the name of your Wi-Fi
- Substitute $wifi_password in psk line with your Wi-Fi password
Booting Raspberry for the first time
Just put the SD card that we just prepared into your Raspberry, connect it with ethernet cable to your router and plug in the power.
CAUTION it is advised to firstly go through all steps below before opening ports on your router!
CAUTION if you have port 22 open and pointing to your Raspberry then it will be accessible through the internet and anyone can log into it with the default credentials!
If all went well your Raspberry should now be connected to your local network, either via eth0 or Wi-Fi. Give it a minute to boot properly and log in
Using SSH to access your raspberry
Finding your Raspberry IP
Consult the manual of your router on how to log into the admin panel and in device list search for device named “raspberry”
Connecting on Windows
You can connect via PuTTY. In host name put the IP of your Raspberry on local network, make sureto select the SSH connection type.
Connecting on Linux
Open a terminal window and use the following command
ssh pi@$RASPBERRY_IPSubstitute $RASPBERRY_IP with your… Raspberry’s IP address on your local network.
In case you do not have an ssh client installed run the following command first
sudo apt install opensshBonus – Android
It is also possible to log into your server via phone. Your smartphone can allow you to remotely access the server just like any other computer can. I cannot recommend in good faith going through this tutorial series on your phone but it is possible as well. It can, however, be used to remotely reboot a service, access a log, add a user or just check up on your server. I am currently using habilis’ dynamic MOTD and after I log in I get presented with basic information regarding the health of the server. Should you need it, you can shut down the Pi as well – bear in mind that a power cycle is needed for a boot after a shutdown.
In case you are interested, look for SSH client on Play Store or AppStore. A good choice would be Juice SSH. It has a premium version but basic is useful as well, I never felt the need to upgrade to premium.
First time login to your Raspberry Pi
The default credentials for logging in are as follows
user: pi
password: raspberryWe will be creating a new user and deleting the default one shortly
Updating raspberry
Before we do anything, we need to make sure our server is up to date. Run the following commands answering y to all prompts
sudo apt update
sudo apt upgrade
sudo apt autoremove- update – updates the repository cache files, which tell our server what packages are available, in which version and what are their dependencies
- upgrade – actually updates packages that you have currently installed on your system to their newest versions
- autoremove – should a package installed automatically become useless i.e. no other package depends on it any longer, either because something got uninstalled and it orphaned said package or it became obsolete, this command will remove any such packages
Creating a new user
Now we can add a new user that we will be using instead of the default user pi. Since it is a well-known user you might be at risk of a security breach if you fail to at least change the password. It is best, however, to just delete pi instead, you really do not need it. We will do that in a moment. For now run those commands to create a new user and add it to video group
sudo adduser $NEW_USER_NAME
sudo usermod -aG video $NEW_USER_NAMEApart from the new password, which should NOT be 12345, you can to input some basic information about the new user. You can safely ignore it and just press enter every time and confirm with y at the end. It does not matter to us, unless you know why that matters but then you would not be reading this guide.
Adding our new user to video group enables the usage of vcgencmd commands to e.g. check CPU temperature, failure to add that user to video group will result in errors while using vcgencmd. It is not important to normal users e.g. email account users that we will create later, but add it to your main administrator account for good measure.
adduser vs useradd
We have two commands available to us to add users. adduser, which we used, and useradd – this one should be avoided. The difference is that adduser creates a home directory and copies default files there for the new user. useradd does not. At a later stage, when we will be setting up the email server, we will also create a basic skeleton of the mailbox folders in /etc/skel so that any subsequent users we create will have them enabled and copied to their folder by default. Skeleton and /etc/skel – ha-ha! Am I right? Nothing?
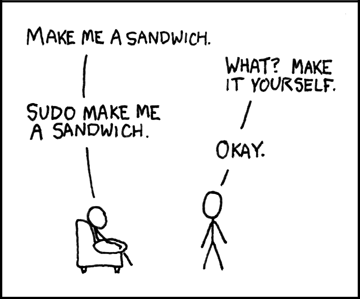
Allowing the new user to use sudo
By default root account is disabled on Raspbian. Good, we do not actually need it, and 99% should be done with normal account using sudo command anyways. Sudo stands for superuser do – act as the highest authority on the server. All configuration modifications, reading logs and many more things require root privileges – hence sudo!
We have two straightforward ways of enabling a user to use sudo. Either we can add the new user to sudo group or run visudo command.
Adding the user to sudo group
This is easy and you probably already figured out how to do it, just type the following command
sudo usermod -aG sudo $NEW_USER_NAMEThe drawback is that you will be asked for password when you use sudo the first time during the current session. It is a preemptive measure for that time when you leave your desk with the terminal window open – only your files are compromised and not the whole server. Usually this is the best choice of enabling sudo.
Using visudo
Another way is to use visudo command. This modifies the file telling your system who is the boss around here, so to speak. Be careful as erroneous dealings here might break everything you already did so far! As we have no way of logging in as root you would have to start the whole installation process anew!
visudo modifies the /etc/sudoers file that normally is only readable to the root user. By default even root is not able to write to the file. You can check out the contents of the file running the following command
sudo cat /etc/sudoersNow that we know what we are modifying let us get on with it.
To access visudo run the following command
sudo visudoFind the following line
ROOT ALL=(ALL:ALL) ALLDirectly below, in a separate line add the following
$NEW_USER_NAME ALL=(ALL:ALL) NOPASSWD: ALLSubstitute $NEW_USER_NAME with the name of the user you created, save and exit. visudo parses the file before writing it to sudoers and checks for errors in case you make an unrecoverable mistake. If you make such a mistake after saving and closing the file it will ask you what to do. type e to edit the file again or x to exit discarding changes.
Now you have a user that can act as root (superuser) using the command sudo. The NOPASSWD: bit is there so that you are not asked for password when using sudo. I do not recommend adding it in a live situation, again – a potential security breach. Linux, in contrast to Windows, is all about security.
Acting as root
If for some reason you actually need, or want, to become root run the following command
sudo su -You will notice that Bash shell changed colors to reflect that you are acting as root and stopped helping you with flashy colors. That is to tell you to be careful. You can stop acting as root by simply typing exit in the command prompt.
Basic configuration of Raspbian
Now it is a good time to use the raspi-config tool that enables us to modify some system settings. Run the following command
sudo raspi-config- Navigate to 2 Network Options and change N1 Hostname to your FQDN (domain name)
- Now go to 3 Boot Options and change B1 Desktop / CLI to B1 Console
- Navigate to 4 Localisation Options and set up correct settings. You can skip wi-fi even if you are using it, wpa_supplicant.conf took care of any settings we might want to change here
- Navigate to 7 Advanced Options and select A1 Expand Filesystem
- OPTIONAL In advanced options select minimal memory split for video, you don’t need that
- Select finish, if not prompted for a reboot, reboot now running the following command
sudo rebootFQDN stand for Fully Qualified Domain and it should reflect the domain you are going to use. If your domain is example.com then this is what you should put there. It will be used by postfix email delivery agent later on
As mentioned earlier we only require CLI (Command Line Interface) and resources needed to run desktop environment (GUI) can be used elsewhere.
Raspbian defaults to UK standards. Changing to en_US.utf-8 is the most versatile option. Keyboard options are changed so that you can use special symbols on your keyboard and local letters
Expanding the file system will make sure you are using all the available space on your SD card.
Log in with the new username and test sudo
After a reboot, connect to your server via SSH like you did previously, however this time instead of using pi username use the one that you added. Once you are logged in run the following command
sudo apt updateIf you are able to update the repository and server is not asking “Are you root?” then all is fine and we are almost done with setting up our server. If something is wrong check out previous paragraphs of this tutorial.
Deleting the default user
Now that we have everything set up, including our new administrative account we can get rid of our default user pi. To do that run the following command
sudo deluser piCAUTION It is important to delete and never use the username pi as it is a default Raspbian account with sudo privileges. Should someone log in with pi username the intruder will have access to all data stored on your server and can break your machine after stealing all your data. Yeah that’s gone now… During the next step we will secure our server, but logging in as pi will not be considered an attack, intruder had all the credentials needed, and will not be prevented. Think of it as leaving your house keys on a sidewalk with the address attached to it. Server hardware can be checked and it shows that it runs on Raspberry.
Conclusion
Right now we have a working server with a new user. Tabula rasa so to speak. We can now order it to do whatever we want. But before we do that we need to secure it and open to the world. Stay tuned for the next part on tightening security. Deleting the default user is just not enough.
Feel free to drop a comment if you spot a mistake somewhere or if a software update made a part of the tutorial obsolete and in need of updating!
